Phish in a barrel
Preface
Our Cyber Lab and Red Team have conducted a range of phishing-related R&D since the beginning of the year, and recently presented some of this research at the CyNam conference. We were also due to deliver a longer presentation and demo of phishing at the ESRM Conference, which was postponed in response to the Coronavirus outbreak.
Given the current trend for phishing content exploiting the present health situation, we thought it worth getting out some more information in the form of a blog. We’ll shortly have some more specific research out on the rise of targeted phishing campaigns.
The Threat
This section shouldn’t need to exist as everyone should know it by now; but anyway, let’s talk about the threat of phishing.
Pretty much any breach report you read has phishing at the top of every chart of attack trends. For example, take Verizon’s last breach report that has phishing as the top threat action across the analysed breaches:
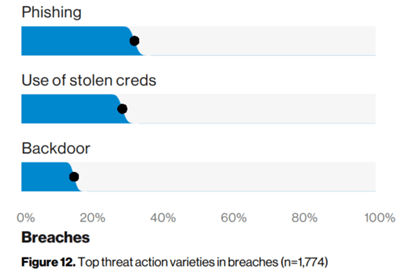
Threat Actions in Breaches, Verizon 2019
And another example reported in the NCSC’s 2019 Breach Survey, which has phishing in 80% of all breaches:
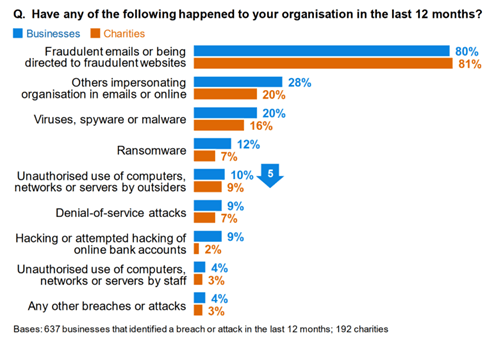
NCSC Breach Statistics
That’s probably more than enough. Everyone knows phishing is massive, so what’s new?
What Has Changed?
Let’s classify traditional phishing as the sending of malware or some kind of nefarious content, such as Microsoft Word documents containing malicious macros. This kind of traditional phishing is still very much an issue, and it does still largely consist of malicious Microsoft Office documents, but it no longer encompasses the whole threat. More than half of all phishing emails represent the other threats: efforts to simply steal credentials or to extort money from victims.
Stealing Credentials
A whole swathe of attackers don’t care about gaining access to a computer or network, they’re just after stealing login credentials. A significant proportion of phishing emails contain malicious links that go to spoofed login pages for various online services. Malicious links are not just restricted to phishing; Symantec state that one 1 in 10 of all URLs are malicious.
The end-goal is typically stealing a user’s password, and often forwarding the same malicious email to the user’s contacts. Stolen credentials are sold in bulk, with whole sites on the Dark Web devoted entirely to this trade. For example, here is a screen shot of the Dark Database Marketplace, selling dumps of stolen credentials for the Bitcoin equivalents of $100 and up.
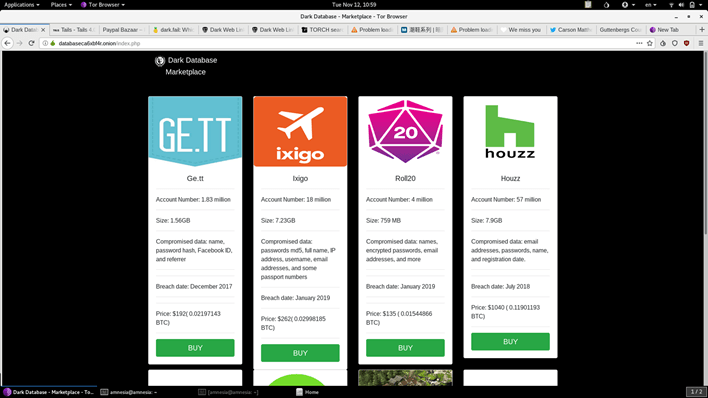
Dark Database Marketplace Dump
Extortion
A growing threat to businesses is Business Email Compromise (BEC). To be clear: growing doesn’t mean it is not already a massive problem; The FBI reckon it accounts for half of all costs related to cyber crime, costing an average of $75,000 per incident. It is grouped with phishing as it uses email, but really it’s straight-forward social engineering, where the attacker uses email to fraudulently convince a victim to make financial payments and transfers.
One of the most high-profile incidents was Nikkei America, who lost $29m to fraudulent bank transfers as the result of a BEC. It’s not all fake invoices and changes of bank account details, a smaller-scale but more common approach is emails asking for the purchase of gift cards.
Similar to BEC is the rise of sextortion emails, which look to blackmail individuals into making payments, typically in BitCoin, in exchange for not releasing supposedly compromising data on the individuals. Here is an example that we received:
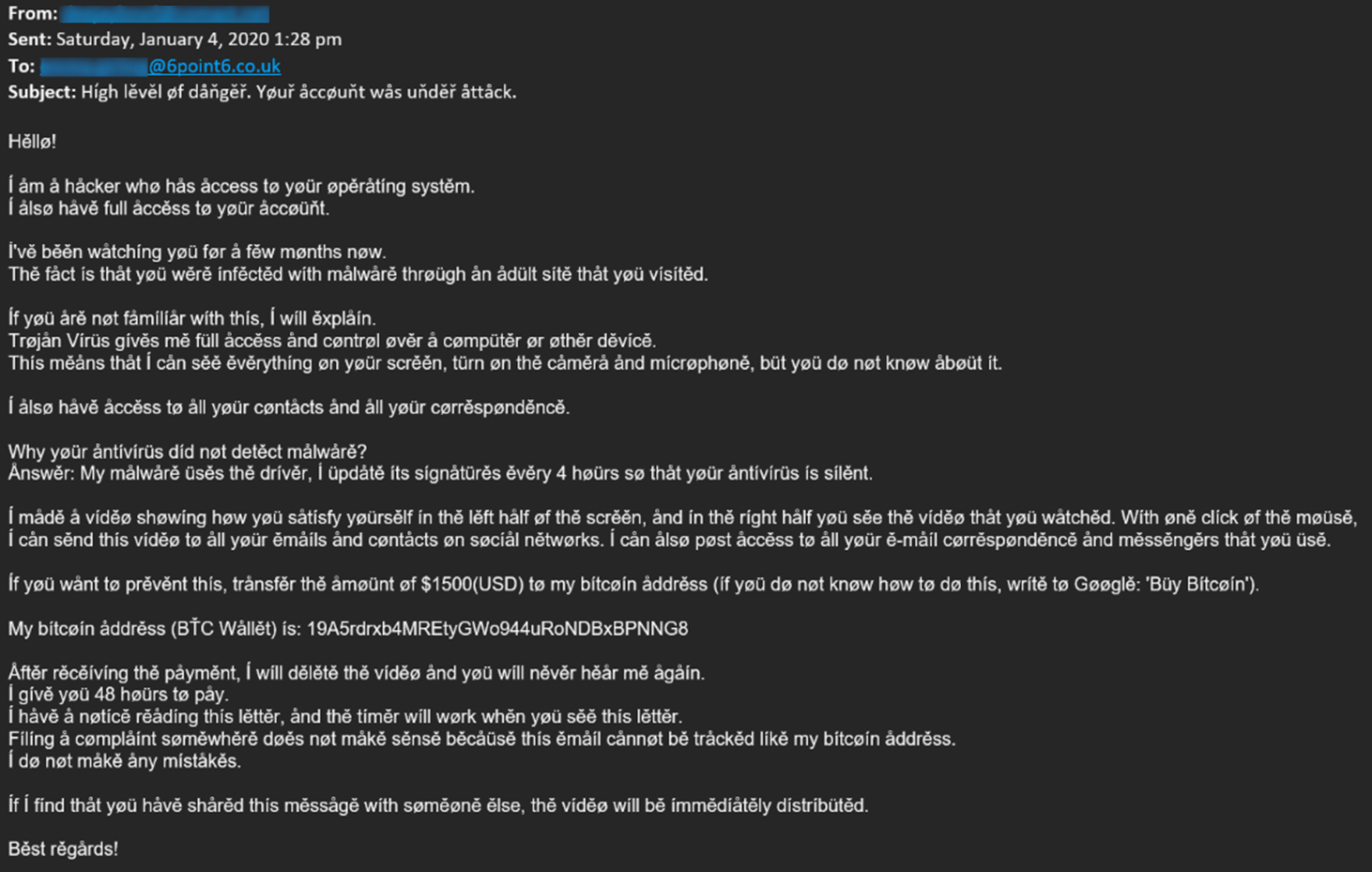
Example Sextortion Email
This one is fairly typical in its content, and is presumably using the odd font as an attempt to confuse content filtering.
Looking at the BitCoin wallet mentioned in the email shows regular inbound payments, and withdrawals to tumblers that presumably are in use for laundering purposes.
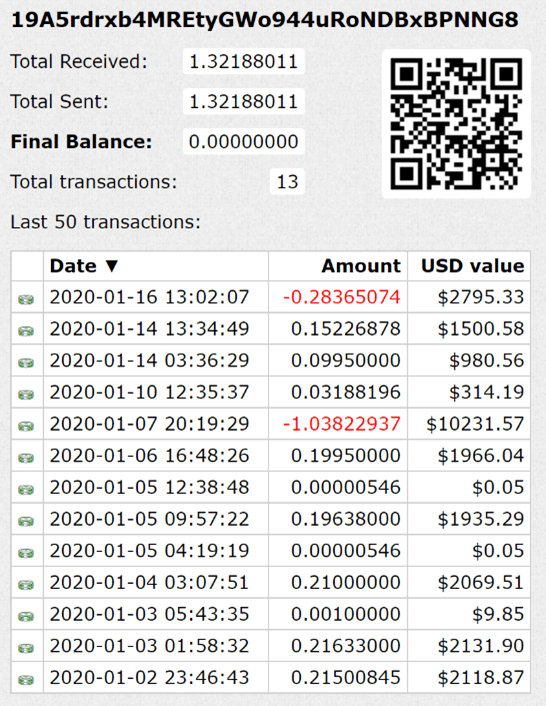
Bitcoin Wallet History
It is fair to assume the vast majority of these are baseless and are just playing on people’s vulnerability; your average scammer doesn’t have the capability to do what they claim, such as a drive-by-download of malware from a porn site that captures images from your webcam.
Finally, just to underline the point that individuals are as much a target as organisations, there is romance fraud, against which the City of London Police have several initiatives.
How Easy Is It?
Setting up a phishing capability is very easy. Our Red Team phishing capability was built for almost no cost, using an open-source phishing platform and webserver. Other than cloud hosting, the only thing we paid for was an email relayer service, which was purely for convenience as it was only $14. There is no reason why you have to do it all yourself, particularly if you’ve some Bitcoin and the Tor Browser: This blog from Digital Shadows puts actual prices on phishing capability sold on the Dark Web.
One advantage we have in being on the side of the good guys is that we can speak to people about what we are doing. One domain we registered was flagged as being likely malicious, but a quick email chat and ID check got it unblocked.
What Should I Do?
Traditional phishing services focus on user education. Whilst that should always be considered, it seems unfair to put the burden on users, as people are always going to click on links. The focus for user training and testing should be on positive reinforcement. Rather than shaming people who have clicked on a link, accept that there will always be clicks, and instead promote good behaviour like reporting suspicious emails.
A potential idea for increasing awareness without using negative reinforcement is to start an interactive means of communication, for example a Slack channel, to discuss phishing in general and report potential threats. It allows people to talk more openly and without judgement about phishing, in a more interactive manner than a security email address.
Emphasis should also be placed on the proper endpoint tooling, to protect the users in the case of successful campaigns. Detection of malicious emails, websites and documents is paramount to protecting the users.
Organisations using cloud services benefit from some inherent improvements to phishing defences, assuming they are correctly configured. Firstly, there are more protections built into the cloud platforms. Secondly, using a webmail application renders traditional phishing with malicious content moot.
Lastly, for more traditional domain-based networks, CISOs and IT administrators should think about infrastructure protections, defensive protections, and end-user device hardening.
Thanks to John O’Mahoney from our Red Team for some of the research, and all of the title. For our latest research, and for links and comments on other research, follow our Lab on Twitter.