Analysis of nanocore RAT
Our Cyber Lab received a request to analyse a potentially malicious file attachment which was distributed via email to a client. The malicious file was first statically analysed and then deployed in a virtualised environment to observe its behaviour. The following report below details the results of this analysis, and contains the following information:
- The processes used to analyse the malware.
- A summary of the history of the malware and it’s known behaviour.
- The behaviour we observed when analysing the malware in our own virtual environment.
Delivery and extraction
The malware arrived via an email attachment and was flagged by local anti-virus software. The malicious attachment contained a single disk image .img file, inside of which is a Windows Portable Executable (PE) binary.
Malware details
| Filename: | Recent Invoice.img |
| Targeted OS: | Windows NT 32-bit |
| SHA-256 Hash: | 942473d08b97bd32b38cdbd4d598e6af509881493785770a3d1c513f8e6d8ca6 |
Analysis and identification
The PE binary was extracted and uploaded to VirusTotal for initial automated static and dynamic analysis. 41 out of 69 antivirus engines positively identified the file as malicious software, with almost all of them identifying the file as a variant of the Nanocore Remote Access Trojan (RAT). The behaviour observed in our own virtualised analysis also suggests we are dealing with nanocore.
When deployed in a virtualised Windows environment the malicious binary exhibited the following behaviour:
- Malicious file creation and modification.
- Malicious process creation and injection.
- Registry access by the malicious process.
- Connections to Command and Control (C2) servers.
Nanocore RAT history and features
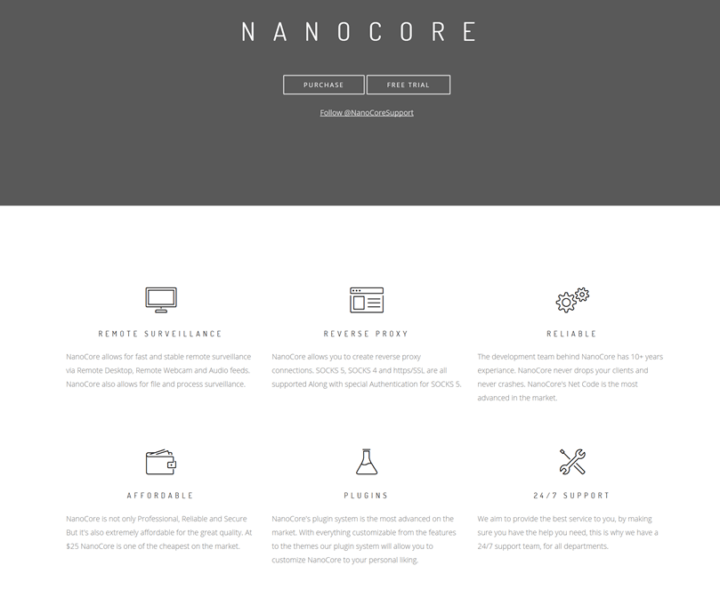
Nanocore is a Remote Access Trojan which first appeared in 2012 and was originally sold by the author for $25 on his website nanocore.io, with the author selling his tool under the guise of a ‘Remote Administration Tool’. The website boasted the software to have the following features:
- Remote surveillance via Remote Desktop, Remote Webcam and Audio feeds.
- Reverse proxy connection capability.
- Affordability, with a price tag of $25.
- Plugin support.
- 24/7 support.
The plugin list is extensive; a few of the plugins available are listed below:
- Surveillance plugin: Allows for microphone and webcam access.
- Tools plugin: Allows for better control over the compromised host.
- Security plugin: Provides access to the compromised host’s AV tools and firewall.
The author, Taylor Huddleson, was eventually arrested in 2016 and in 2018 sentenced to 33 months in prison.
Behaviour summary
- Nanocore first creates persistence by copying itself to the Windows startup folder.
- It then launches the legitimate RegAsm executable file which is later injected into. The purpose of the injection being to mask itself as a legitimate process whilst running.
- Finally, it starts encrypted communication with the Command and Control server where it waits for commands.
Analysed behaviour
The following is a time-specific breakdown of the behaviours of the malware sample:
- Time 403ms: The first action the malicious.exe process carries out is to create an exact disk copy of itself called filename.exe, in the folder %APPDATA%\Roaming\.
- Time 422ms: Again the process creates a copy of it’s disk image (malicious.exe) called hjdytuap.exe in the Microsoft startup folder %APPDATA%\microsoft\windows\start menu\programs\startup\hjdytuap.exe. (Note: Storing the malware in the startup folder allows for persistence between reboots.)
- Time 11547ms: The legitimate Windows process, RegAsm.exe located at C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe is then launched by the original malicious.exe process. (Note: This is in preparation for later when the malicious exe process injects itself into this legitimate RegAsm.exe process where it continues to run, adding an element of stealth.)
- Time 11719ms: It then launches cmd.exe with a command line argument to delete the original malicious exe file on the disk and creates another instance of itself
- Time 11211ms: The original malcious.exe process then injects malicious code from itself into the legitimate RegAsm.exe process launched in step 3. (Note: RegAsm is a legitimate program. From Microsoft documentation “The Assembly Registration tool reads the metadata within an assembly and adds the necessary entries to the registry, which allows COM clients to create .NET Framework classes transparently.”)
- Time 12250ms: The compromised RegAsm process then creates an 8-byte file called run.dat in %APPDATA%\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\run.dat
- Time 12953ms: The RegAsm process then carries out a DNS request to google DNS servers at 8.8.8.8 to resolve the domain duckdns.org cbswgc.duckdns.org (Note: Duckdns is a service which allows a user to create a randomly generated duckdns subdomain and have that subdomain resolve to an IP of the user’s choice. This allows the malware to indirectly resolve a domain name to an IP address.)
- Time 13960ms: Duckdns gives us back an IP address of 192.169.69.25. We then carried out a reverse IP lookup and found it resolved to the domain name sinkhole.hyas.com. (Note: The IP address indicates that the server is located in the USA. Looking this domain up on abuseipdb.com (contains information on malicious IPs), we find that the IP has been reported twice for spam/malware.)
- Time 13960ms: Once this IP is resolved, the RegAsm process proceeds to send an encrypted 60-byte TCP packet to 192.169.69.24 over port 4842.
- Time 27272ms: RegAsm then resolves another duckdns subdomain (fbpa.duckdns.org) using google DNS. (Note: This time the IP resolved is 194.5.98.239. This IP address indicates that the server is located in Poland. A reverse IP lookup on this IP shows that no domain name is associated with this IP address. We can assume this is one of the C2 servers for the Nanocore RAT.)
- Time 27269ms: From here, RegAsm continues to contact the C2 server using encrypted traffic
For our latest research, and for links and comments on other research, follow our Lab on Twitter.